Hello Team,
How do you setup a 2FA on the n8n local server? I saw some mentions about it but so not see any option for that.
Hey @kgurinov,
n8n doesn’t directly support 2FA at the moment, You may be able to work around this using a third party authentication provider like Keycloak but I am not aware of any instructions on how to actually do it.
Hey Jon, is this on the roadmap? Is it expected to be added any time soon?
Hey @joeldeteves,
Looks like you have put a note on all of the 2FA and SSO request ![]()
It is something we want to get done and it will happen but there is some additional background work that needs to be sorted first.
I sadly don’t have any timeframes for this one though.
Yes this is an extremely important feature. Security should come first. I’ll go ahead and cast my vote. Thanks Jon,
Hi @joeldeteves
You can probably fix this with cloudflare zero trust. I haven’t tried this but should work I guess.
i use cloudflare zero and have 2fa enabled, works perfectly.
Thank you @RedPacketSec we use a Traefik proxy so I’m looking into using Forward Auth as well. Good to know it works behind Cloudflare; did you need to do anything special for external automation services? Or do the webhooks get excluded from this?
So I created something of my own using oauth2-proxy as an interim stopgap solution.
The downside to this approach is that it requires a “double login” - so, it’s good for a temporary ‘two’factor’ but it’s also a pain, as I have to use both my AAD login and the N8N login.
I guess what I’m saying is native support for SSO + 2FA would be the best option in the long run.
(New setups can get around this by skipping the user setup as per the docs. That won’t work in my use case since I’m already setup and have workflows and don’t want to re-deploy from scratch).
EDIT 2: It would seem this has broken the webhooks as I feared. So it looks like I’m back to square one.
EDIT 3: I was able solve the second issue by excluding the following path prefixes:
- /webhook
- /webhook-test
I suppose I could have set the WEBHOOK_URL variable and used a single path prefix, but I like this solution better since it means I don’t have to recreate the hooks in my existing workflows.
Hi @joeldeteves
You should be able to disable the n8n login. Would probably be done by changing some values in the database. Not sure which ones but should be fairly easy to try.
Yes, I was using a similar approach in the past, simply letting my reverse proxy handle the authentication (using caddy + caddy-security), excluding the webhook and API paths. This worked fine.
The environment variable suggested by @BramKn would be N8N_USER_MANAGEMENT_DISABLED=true, you’d need to configure it before setting up user management though, so it might not be what you’re after. You could try resetting your user setup using the n8n user-management:reset CLI command though (it’s worth taking a backup beforehand, just in case).
Wouldn’t it also be possible (if the command does not work) to simply “hack” the database? ![]()
Oh, I read environment variable instead of database, not sure what I was thinking ![]()
Yes, you can probably hack the database too, though I haven’t done this
Thanks @MutedJam. I followed these steps:
- Backed up my SQL database
- Exec’ed into the pod
n8n user-management: reset- Set
N8N_USER_MANAGEMENT_DISABLED=true
Now I can log in using my Azure AAD without also being prompted for N8N login!
This is a great workaround until native support gets added (I do hope it will be added at some point so we can have multiple users).
Thank you,
Can you help me to get the webhook excluded?
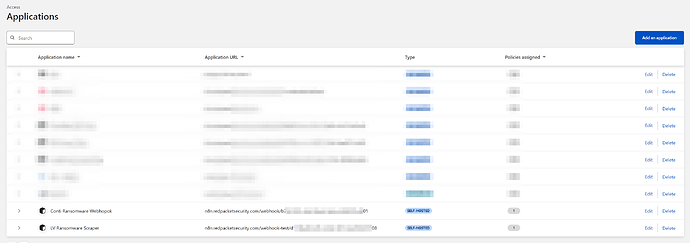
sure, you need to login to the cloudflare teams dashboard
goto applications
then set your policy and requirements to allow access, e.g bypass waf or only allow from certain IP address etc,
So you bypass the whole webhook address not just the /webhook or /webhook-test?
yeah i use the whole url, and set a bypass if I am unsure where the requests are coming from, depending on the type of cloudflare account you can add additional checks such as header checks etc.
or I set an allow rule if I am using a specific service and IP range.