Describe the problem/error/question
Hey community,
I am trying to read info through Microsoft Graph. I have the Azure app setup with Application permissions for the scopes I need, but I am struggling to get the credentials working in n8n.
I think I have everything according to the documentation:
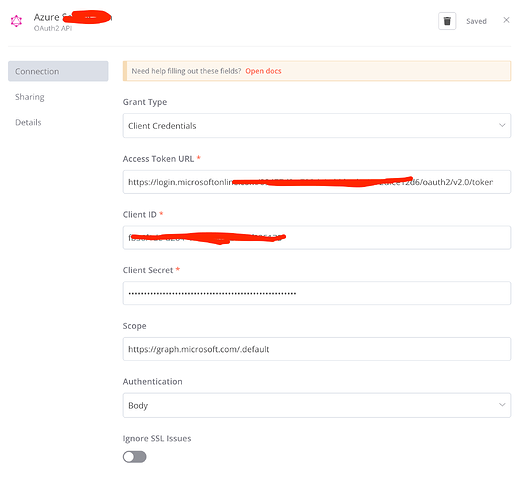
n8n Oauth Credential settings:
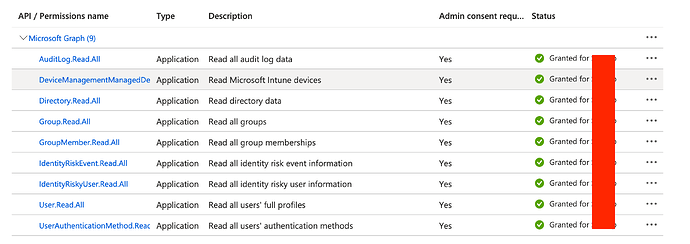
Scopes for the Azure App
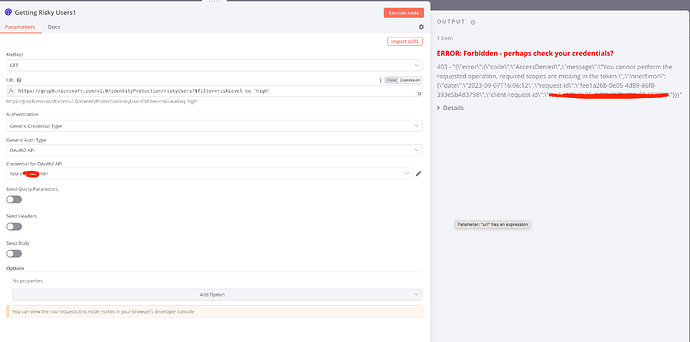
HTTP request for risky users - requires IdentityRiskyUsers scope:
According to the error it seems like a problem with scopes, but according to the docs https://graph.microsoft.com/.default should give it all the scopes from the app.
I tried the same credentials via python and it all works fine.
Anyone could help (for example @pemontto according to a different post have it working), I am lost at this point.
Thanks
What is the error message (if any)?
Please share your workflow
Share the output returned by the last node
"403 - "{\"error\":{\"code\":\"AccessDenied\",\"message\":\"You cannot perform the requested operation, required scopes are missing in the token.\",\"innerError\":{\"date\":\"2023-09-07T16:06:12\",\"request-id\":\"fee1a26b-0e05-4d89-86f8-393e5b483798\",\"client-request-id\":\"fee1a26b-0e05-4d89-86f8-393e5b483798\"}}}""
Information on your n8n setup
- n8n version: Cloud 1.4.1
- Database (default: SQLite):
- n8n EXECUTIONS_PROCESS setting (default: own, main):
- Running n8n via (Docker, npm, n8n cloud, desktop app):
- Operating system: