I’m setting up SAML authentication with Okta for n8n Business Edition (self-hosted on Kubernetes using Helm) and facing some issues.
When I try to log in via Okta, I get this error:
{"code":401,"message":"SAML Authentication failed: SAML Authentication failed. Could not parse SAML response. ERR_IDP_METADATA_MISSING_SINGLE_SIGN_ON_SERVICE"}
Here’s what I’ve tried:
-
Initially, I set the environment variable:
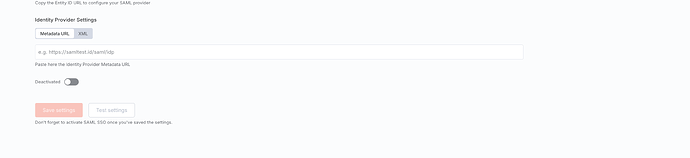
N8N_SAML_METADATA_URL=https://org.okta.com/app/**********58/sso/saml/metadata But the metadata URL did not appear in the IdP metadata field in the n8n admin UI. -
Then, I created a ConfigMap with the downloaded Okta metadata XML and mounted it in my deployment:
N8N_SAML_METADATA_PATH=/home/node/.n8n/public/static/okta-metadata.xmlI can see the XML file inside the pod, but the IdP metadata field in n8n UI is still blank.
-
If I manually upload the metadata XML or URL in the n8n UI, SSO works — but whenever I redeploy or update my Helm release, that field resets to blank, and I get the same error again.
I’ve also set the following environment variables:
N8N_SAML_LOGIN_ENABLED=true
N8N_SAML_METADATA_PATH=/home/node/.n8n/public/static/okta-metadata.xml (when using Metadata XML)
N8N_SAML_METADATA_URL="https://url" (when using metadata URL)
Could you please let me know how to persist the IdP metadata (URL or XML) via Helm configuration, so it survives redeployments and works automatically with Okta?
Reference documentation : Okta Workforce Identity SAML setup | n8n Docs