Describe the problem/error/question:
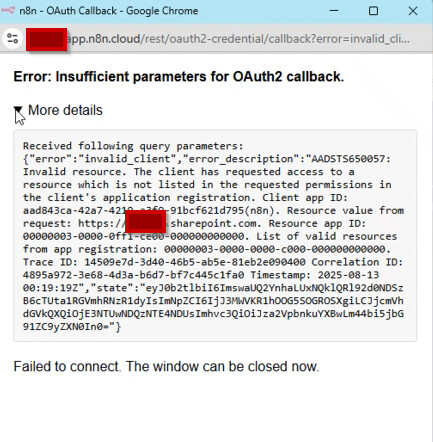
We are consistently getting errors whereby we are unable to authenticate for SharePoint within our n8n tenancy. We have fully removed the n8n enterprise app from the tenancy and have tested on separate n8n instances and are still experiencing the issue.
What is the error message (if any)?
The app is removed from the tenancy , yet we still receive the above - any assistance will be greatly appreciated.
Information on your n8n setup
- n8n version: 1.99.1
- Database (default: SQLite):
- n8n EXECUTIONS_PROCESS setting (default: own, main):
- Running n8n via (Docker, npm, n8n cloud, desktop app): n8n cloud
- Operating system: Windows 11