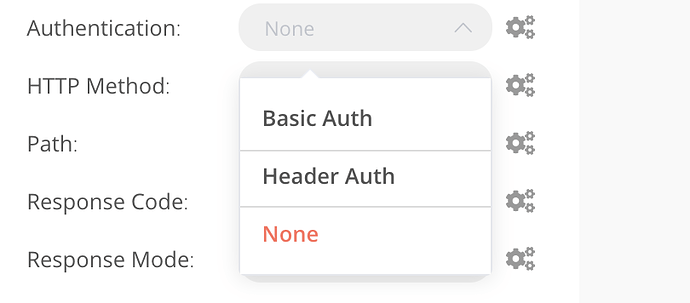
On the “Webhook Creating Endpoints Part 2” video on YouTube, a proper way to authenticate users is mentioned but not described. What is the proper way to secure Webhooks on n8n?
Ricardo,
there are other Auth Methods in Pipeline ? OAuth ? Or do we need to implement this via Proxy ?
Thanks,
Stefan
We have many more authentication method in the HTTP node. What do you want to do exactly?
Been trying to Basic authenticate a POST webhook in test-mode from self-hosted Seatable.
Wasn’t able to find an example on either the documentation or the forum, though I’m probably not the first doing this.
I thought this would be enough:
const username = "n8n-basic-auth-USER";
const password = "n8n-basic-auth-PASSWORD";
let data = {
row_id: base.context.currentRow['_id']
};
await fetch(url, {
method: 'POST',
credentials: 'include',
mode: "no-cors",
headers: {
'Content-Type': 'application/json',
'Authorization': "Basic " + btoa(`${username}:${password}`)
},
body: JSON.stringify(data)
}).then(res => {
console.log('Request complete! response:', res);
});
I get a 403 Error and been looking at specifications for a while now, trying different things.
It’s probably an easy fix, one suspicion I have is that the request from Seatable Javascript script originates from seatable.mydomain.com and goes to n8n.mydomain.com and gets rejected?
In n8n I have set my Basic Auth credentials with User = ‘n8n-basic-auth-USER’ and Password = ‘n8n-basic-auth-PASSWORD’ (in reality a 44-character string with uppercase, lowercase, digits).
Without authentication it works fine, so I guess I’m fucking up somewhere essential and can’t see it right now : D Any pointers would be much appreciated!
Information on your n8n setup
- n8n version: 0.193.5
- Database you’re using (default: SQLite): Postgres
- Running n8n with the execution process [own(default), main]: main
-
Running n8n via [Docker, npm, n8n.cloud, desktop app]: Docker
Using traefik as a reverse proxy.
Not using user management, but Basic Auth for logging into my n8n.
Hi Ricardo, That a Webhook Endpoint in N8n can use Auth Method OAuth2. What do you think ?
Regards,
Stefan